DEF CON 31 - Snoop On To Them, As They Snoop On To Us - Alan Meekins
Wonderful. Thank you. All right. Thanks for having us. So today's talk is snoop unto them as they snoop unto you. I'm Alan Meekins. I go by nullagent on most social media, Twitter, Musk on, all that good stuff. You'll find me as sevenbitbyte on GitHub. My personal website is actually kind of blank, so I'll try to fix that this week. I've got a co-speaker, rekchadam, who couldn't be here today. He's stuck in Tokyo without a passport. We've got 5@V@g3, our apprentice here today.
So just quick background, big robotics nerd, embedded systems, been playing with Linux since I built my first computer, really love digital communications, which this talk is going to touch on a lot today. I occasionally do, I guess, grownup work, but these days I am recklessly unemployed and founder of Dataparty. So we're basically a hacker collective looking at the intersection of just media and all the things that hackers love. So today, the thing that got me started thinking about this was actually a lot of police interaction that my co-founder and I had over the years. He grew up going through high school getting pulled over by the cops basically every day. Growing up we were hearing a lot about no-knock raids. Coming from a hacker's perspective and seeing things like no-knock raids,
you kind of start wondering WWLND, what would Lord Nikon do? So Lord Nikon would probably take a closer look at the boys in blue and maybe what they carry and how they operate. To give you some idea of what the landscape is like on the digital world of a cop, they have on the left, the things that they carry, typically tasers and body cams, a smartphone, pistol. Things in the middle that certain companies wish they might carry maybe, flying drones with tasers on them. And then on the right, we have all the things that are in their vehicle, Wi-Fi hotspots, surveillance systems that can actually do license plate reading. So they actually do ALPR coming soon on their dash cams. Of course, they've got a laptop and they have these weird little boxes called Axon Signal. So if you remember the movie Hackers, one of the
big things that they talk a lot about is reading the manuals. So first step was just see what was out in the open. And so, if you start reading through the manuals for all of these types of equipment, you'll see a whole bunch of terms like Cradlepoint and NetCloud mentioned. You'll see things like Bluetooth pairing and you'll see brand names like Axon Signal, and then occasionally you'll find some really cool things like, "Hey, this is exactly what an error state looks like, and here's an exact network map of what a police car looks like inside." You keep reading, and before you know it, you find all sorts of URLs that look tasty and delicious and could be interesting. So if you ever talk to public defenders and those sorts of people, they hear about this thing called Evidence.com, and a lot of them don't realize that that's
actually built by the same folks who make the body cams themselves and all the digital tech. It all just funnels up to this cloud. So they typically access it through their agency name or their city or state or something, .evidence.com and consume content. And then if you keep reading, you'll start seeing some interesting things that might get a hacker's eyebrows open a little bit. But at the end of the day, the thing that really caught my eye is that the boys in blue are actually... Or actually just kept a couple things, so Wi-Fi access points and fleets and so on, but the boys in blue are actually the boys in BLE.
So there's a term that keeps happening a lot called Axon Signal, and I keep seeing the word BLE co-occurring with that in the documentation. So just a quick trip down memory lane from DEF CON is when we're talking about hacking the planet on the terms of BLE, there's been a great talk by Freqy at DEF CON 29 where she explained a lot of basic BLE, the basics of BLE, how BLE pairs, how it interacts with the host and so on. It's a great starting point to understand what might be going on under the hood of some of these products. If you keep reading further, you might see some things like Handoff All Your Privacy, which deals with how Apple has a BLE protocol called Apple Continuity. You might also see some things called You Better Secure Your BLE Devices, which has a lot of parallels to what we're seeing today. And then lastly, Mike Spicer did a talk called I Know What You Did Last Summer.
So just a quick refresher on BLE, I'm not going to go crazy deep on BLE fundamentals, but A BLE device needs to allow the other devices that it wants to pair with to know that it's around. So they send out these broadcasts, these beacons a lot like how Wi-Fi access points also beacon out. Typically, you'll find these types of parameters inside of there, at least a MAC address. And then basically everything else is kind of optional, so manufacturer data services,
products, company, local name, RSSI, possibly like URLs and additional what are called gap fields, so additional fields just like this. Of course, you start thinking about if you were to reverse-engineer or to fingerprint device that you haven't seen before, say like a cop device, there might be a whole spectrum of ways that you might approach that problem. So for instance, sometimes gap fields come in different orders. So even two devices from different manufacturers
might have identical data, but they might put those fields in different orders. So that might be a thing that fingerprints or you might go and try to see if you can find things on Wigle.net. Wigle is a big network of war driving that a lot of people who are participating in the worldwide war drive right now, they're currently constantly feeding Wi-Fi and BLE data into Wigle.net. And
then also I built an app called rfparty, which is basically like Wigle in your pocket without a cloud so that you can be entirely off grid, or you could also go down the decompiled apps route. So how can we figure out what these police devices are actually doing? Just as a note, most of the apps needed to manage these police devices are actually currently in the Google Play Store. So you can go download those and decompile them right now. So without doing all of that crazy stuff, how do I do this without violating any kind of permissions or laws or anything? Go back to reading the manual. So I keep seeing this thing called
Axon Signals. So what is that and what does it do? Well, it turns out that the devices highlighted in blue here are actually all Bluetooth-enabled. So body cams and tasers are designed to basically interact with one another. When a taser is fired, certain models can actually send out a Bluetooth beacon that will notify the body cams and the surveillance in cars to start recording or to rather start retaining their recording. Body cams
also have basically shot spotter technology built into them after the third generation or the second generation of those, and they can also detect a gunfire and trigger a Bluetooth transmission. And then third to all of this, the pistol holster itself, there's attachments that can detect when a pistol's unholstered and again, sends out a Bluetooth beacon that is designed to trigger the body cam. The same thing happens on the car side as well. So again, the blue circles here are things that are Bluetooth-enabled. So the documentation indicates that the same Axon
Signal technology is built into dash cams. How are those dash cams triggered? They can be triggered, of course, by everything on the left here, but they can also be triggered by this little tiny box at the bottom that detects when your police lights are falling off of your fan there, and that will actually detect when you turn on your siren when you turn on your flashing lights and send a signal to the recorder as well. And then finally, they have a laptop in the mix that also takes a Bluetooth dongle. I actually never fully figured out exactly why that is because it doesn't seem to actually trigger much on there. And then finally, things that I
didn't even feel like digging into, but they have Cradlepoint Wi-Fi hotspots in there that have all kinds of interesting things in the documentation that I don't even feel like touching today. Yeah. So overall, that's the general architecture of how Axon Signal works. We went through the list of devices that's deployed on. Yeah. So where is it used? Axon has basically their fingers in every part of police life from how do you charge these devices at home or in the office, and also things like interrogation rooms, all of the systems inside of there. Again, that documentation was a little bit more locked down so I don't have as much to share directly on entry points under those systems. So again, with all of this in hand,
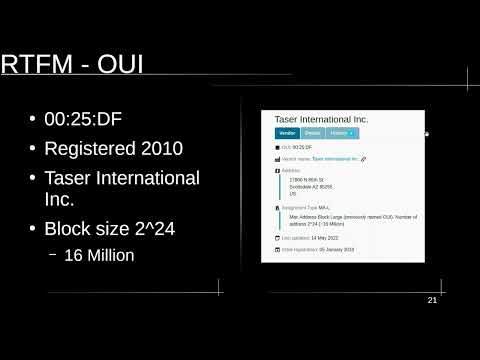
how do you do analysis on this without having to interact too closely? Turns out, go back to reading the manual and there's this thing called an OUI. There's an OUI for the company Axon, which was initially Taser International, called 00:25:DF. That is the first three octets of most MAC addresses in the Bluetooth spectrum. So if you registered an OUI and you want other people
to recognize your device over Bluetooth, you're going to use these in places like potentially in the MAC address itself or in the manufacturer data. You can also have a fingerprint in there. So for my app, rfparty, I actually built a database of over 4,000 device identifiers simply by looking at OUI databases and additionally Wireshark and their database and of course looking at manufacturer data and just from analyzing my own devices discovered that there's a lot of... I'm not sure if things are always on spec as far as how manufactured data gets formatted, but there's a lot of interesting ways to fingerprint your devices just looking at those. So looking at the Taser OUI, you find out that they have a particular block size.
So they've basically allocated 16 million MAC addresses that will be prefixed by this OUI. So since we're talking about broadcast protocols in Bluetooth, a lot of people are very accustomed to when devices are paired. When devices are paired, the broadcast will stop. But there's a growing number of protocols being released lately, which rely entirely on the broadcast capability and basically none at all on the direct connection. So some examples are COVID exposure tracking has a fairly cryptographically secure approach to fingerprinting a person and then fingerprinting or, sorry, having a secure database of exposures that's managed by your local authorities, and then you go and prove it. And then eventually the other people who basically have been around you are essentially war driving when it comes to COVID exposure tracking. They're slurping up all these BLE broadcasts and they're saving the ones that have the correct fingerprint for this protocol, and they're remembering all the public keys of the people around them.
So COVID exposure tracking is another great example. It's one of the most pervasive Bluetooth broadcast protocols, but now it's kind of winding down. So if you look at Wigle data and if you do your own stumbling and whatnot, you'll see that the COVID broadcast have reduced substantially over time. But Apple Continuity on the other hand is
basically second, this is my personal ranking, as far as total traffic that I see. Apple Continuity has a lot of interesting things that it does. Again, the app that we built called rfparty, we parse all the sorts of things that hand off all your privacy discovered, so things like AirPlay IP addresses. Yeah. Your iPhones are currently beaconing your IP address in BLE constantly. You can get information like whether or not the person's on the phone,
whether or not they're looking at a video, if it's their primary iCloud device. So these broadcast protocols have a pretty pervasive impact on your personal privacy and how trackable you are in public and public spaces and governmental spaces. And then finally, we have a really new broadcast protocol that's coming online next month called DroneID. So DroneID will also operate primarily
in Wi-Fi, but there's capabilities to do it in BLE, as well in Bluetooth. I suspect part of the reason is that the BLE hardware might be more lightweight, more ready to be embedded than some of the Wi-Fi equipment to put on smaller drones. And so, again, on rfparty, we're expecting to be able to parse that type of data. So finally, Axon Signal. Axon Signal fits into this patchwork of prevailing and existing broadcast protocols. So taking our understanding of broadcast protocols and everything we found in the manual, let's see what we can find. So if you go to Wigle right now and type in 00:25:DF, you'll find on the left we have the locations of police departments, say, in the San Francisco region. On the right, we have the Wigle map of where 00:25:DF returns
have been heard, and it corresponds pretty closely and of course it's clustered along highways that cops probably patrol. So there's a decade or more data in Wigle. If you run these queries, you're going to see that there's a worldwide footprint that you guys in this audience have been collecting and putting on Wigle. So that's pretty dope. So what can we do with this and what are the other ways that we can detect this? So rfparty could hypothetically, allegedly detect these sorts of things. I can't demo that sort of thing. Unfortunately, I haven't been contracted by any police departments to actually do any pen testing on them. So if you know any, let us know. We'd be happy to help you figure out how to improve this. But for a demonstration purposes, it also turns out that GoPro video cameras have
a broadcast protocol that they implement. So I took my GoPro and essentially assumed, "Hey, let's treat the GoPro like a body cam and see what that might look like in rfparty." So here we have rfparty of public space. I verified that my wireless connections are enabled on the GoPro. At this point forward, the GoPro will actually beacon so that my phone can
manage it. The other interesting thing to know about GoPros and their broadcast protocol is that the protocol does not stop when the GoPro has been turned off. The screen is off, but the packets continue to be emitted, and that MAC address, as I've observed on my GoPro, never changes over the course of years. So when I put out my GoPro into Wigle, I didn't see anything lately, but that's probably changed this weekend if I accidentally turned on my wireless connections. And so, if you had a continuous monitor running and when you searched, if you search for the right parameters, so in rfparty where you're looking for the name of a GoPro, what we'll find is the first ping that we receive will show up on the map as a dot. If you click on that dot, you can see all of these packet information, all the service information. I've blurred out
because of course, this is all my actual personal MAC addresses here. We're able to then see where we've crossed paths with that particular device. And so, here I am walking through a park. These are my GPS pings in this ghostly white. And then at the end, I'm going to run the query again and boom, I've discovered that, hey, I initially saw the GoPro somewhere around here, and then its final location was somewhere over here. There's a number of queries that we support like duration
and triggers that are coming soon and alerts and that sort of thing, but you could imagine that if this were, say, a body cam, so this is more of a simulation of if I were wearing a body cam... We actually have more data points along the way, it just doesn't render it on this screen. But you could imagine that you yourself could monitor for your own devices or in the case of cop detectors, or as far as in the terms of Axon Signal, this essentially demonstrates an idea that there might be a way to detect cops. And so, if we switch back, cool, what does this enable? So specifically at Axon Signal, apps like rfparty and Wigle enable us to potentially do things like proof of body cam. So what's proof of body cam? If you read back on some of those no-knocks that I mentioned, and if you read the news in the last couple of years, you'll find out that sometimes police departments can be cagey to release potentially damaging body cam footage, right? It's kind of hard to compel them because they kind of like to beat around the bush of like, "Hey, we're not sure if anyone was there with a body cam. We got to check our
records." They can really slow-walk things. So if you had a way to say, "Hey, I know this MAC address was in the vicinity. I know this MAC address was at a particular event or a particular occurrence of a potential police misconduct," you can more directly light of fire under their butts and more legally be able to specifically inquire about that information in court, right? Other things that hackers probably think about. There was a competition, I think, at Black Hat and DEF CON many years ago, it was like over a decade ago, where people were competing to make kill switches, computer kill switches. So you hit a button and termites your hard drive, or hit a button, the hard drive catches on fire or various things, right? So you can imagine if you're a very enterprising hacker, you might have a cop alert in the Bluetooth spectrum that could trigger those sorts of things. Of course, knowing things like RSSI and receive signal strength that correlated with these devices, you can very tightly detect the distance that a cop is to your computer and the computer could self-destruct automatically, poof. You could do things like identifying specific
cops. So a lot of cities activists will file cases that will eventually put cops on something called the Brady List, so basically a list of unknown police misconduct and bad behavior, bad apples, if you will. You might want to get an alert if you're dealing with a bad apple, or you might want to know, "Hey, I didn't catch that guy's badge number, but turns out I had Wigle running."
Now you can go dig through that database, dig through your own logs, and now you know their MAC address, and you might be able to subpoena for the rest of the information. And then the other interesting thing that organizations like ACLU and EFF currently monitor are things like surveillance. So where does Axon Signal factor into all of this? If all of these body cams start doing facial recognition, for instance, so these body cams actually have 4G LTE connections and they actually can live stream video at any moment and that's... I'm not even talking about the cloud this year, but there's a huge question about what's the prevalence of this technology, especially as we understand more and more about these features, especially like the license plate reader being embedded directly into the dash cam. What if that license plate reader technology gets embedded into body cams? There's not even a slippery slope. It is a Homer Simpson falling down a ski mountain worth of interesting problems here that we might want to understand as civilians or civil liberties how prevalent these technologies are.
So finally, tools like rfparty, we are absolutely inspired by these types of questions, and we really want to enable other people to be able to experiment and learn about these devices. Of course, if cops are trackable, we're very trackable as well with things like our GoPros and our Apple Continuity. How do we verify that any of those devices are actually in airplane mode? If you read the instructions for iPhone, it says turn off the Bluetooth connection, turn off airplane mode. There's not really a great way for an ordinary person to
verify that. What we're also pointing out here is that every device, not just AirTags, every device is an AirTag, right? So we actually need a way to detect all Bluetooth devices. We don't need one-off solutions that only work on iPhones and then take three years for Android to catch up and then leaves everyone who runs Linux completely in the lurch. We actually need a solution for everyone and for every possible device. So that's the talk. Here's some tools. So the biggest tools are used here were the PDF viewer.
The second most used tool was an OUI database, and then finally Wigle.net. And then some other super handy tool is nRF Connect. nRF Connect is the only multi-platform Bluetooth scanner right now that's allowed, because they're actually allowed on the Apple Store. Apple doesn't really allow hacker tools in their App Store, however, they do use the Nordic semiconductor Bluetooth chips. So somehow Nordic got an app in their store. Yeah. So we're building this thing called rfparty. It runs on Android and then it's on Mac, Linux,
and Windows coming soon. And then finally, we have some open hardware as well. And then all of this is open source. You can get it on the App Store and help us get home. Party on, everybody.
2023-09-23 01:55


