"TOR" to Another World? Stefan Mey about Terms, Technologies and Contradictions of Darknet
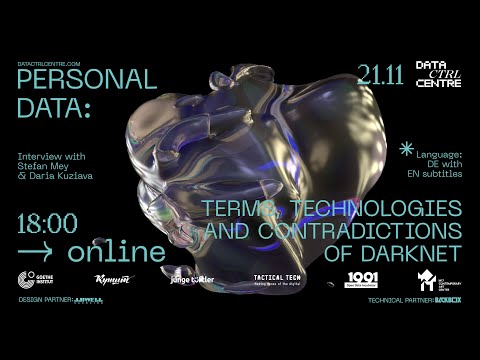
Good afternoon everyone. Welcome to our discussion about Darknet and anonymity on the Internet. I am Daria Kuziava, co-founder of the popular scientific medium KUNSHT from Ukraine. Also, I am the curator of the offline exhibition 'Data CTRL Center'. With me today is Stefan May, a German journalist, a successful book author, and also an expert on everything connected with darknet and anonymity.
Hello! And this discussion takes place within the framework of a large regional project Data CTRL Center, which was initiated by Goethe Institute Ukraine. By this project we want to create awareness of the digital traces we leave behind and how our personal data can be better protected. As part of the project, there is, as I said, an offline exhibition in Kyiv, which unfortunately is open only until November 22. But we also have an online exhibition at the same time that is available in four languages – Ukrainian, Russian, English, and Armenian.
On the website of the online exhibition our online accompanying program will be available. All videos and this discussion as well can be found there, and on the website of Goethe Institute Ukraine. After this brief intro, I think we can get started with our discussion. So, the first question would be What is Darknet? How did it appear? How does it work? And what can you do there? It's a good question! I have prepared some answers.
So what is frankly speaking darknet? There is no fixed definition. I would say that darknet is a place in the big global Internet that shields itself and creates anonymity for everyone involved. There are theoretically different ways to create a darknet. According to Wikipedia, there are 12 different darknets. But one of these darknets has prevailed, namely darknet based on Tor.
You see here a Tor logo. What does Tor do? Tor does only one thing - Tor hides IP addresses. IP addresses are such small columns of numbers; you could say they are something like digital postal addresses.
Websites have always fixed IP addresses. And if you enter a web address in the browser, the browser asks a database, finds out this technical address, and so get the information where the data packets are going. W, being simple users, always get an IP address when we log into our WLAN at home or work or anywhere else. IP addresses are a great thing, they ensure the possibility to communicate quickly and outright. But they also enable surveillance and censorship.
When we communicate, data packets always wander back and forth through the Internet and these data packets always contain information about the sender, the sender's IP address, and the recipient's IP address. That means, my internet provider finds out which website I am visiting, and the website sees my IP address. And authorities who have the right to receive such information can usually convert it into my name quite quickly. For example, secret services that have the right to look into these streams of files, can understand who is communicating with whom, and they can also censor. So my internet service provider finds out which IP address I'm searching for and it can say me "No, I won't allow you to do that". Tor tries to throw some sand in the gears of surveillance, and simply hides those IP addresses.
To make it work, there is a network of several thousand nodes, around 7 thousand nodes, which are spread over half the world. Mostly they are situated in the west, in the politically western part of the world. Interestingly, Germany has the largest quantity of Tor nodes. And when I use Tor, the following happens: the software gets an overview of all nodes that are currently available, selects three of these nodes, and then sends my data traffic there. Firstly, to the first Tor node.
The first Tor node can remove a layer of obfuscation and encryption; it receives the address of the second Tor node. The second Tor node receives the address of the third Tor node, and only the third Tor node knows where the journey is going. This is similar to when I put a letter in several envelopes and each cloaking station can take off only one envelop, the upper one.
Each node only knows its immediate predecessor and its successor, the second Tor node no longer knows who I am and at the same time, nobody knows what is my IP address and what is the destination IP address. That virtually ensures anonymity. There are two applications that use the Tor principle. One is the Tor-based browser; this is an adapted Firefox browser, a non-commercial browser. I'll show you what it looks like and now I'll call up a rather harmless website, e.g. 'Bundesregierung.de.' That looks completely normal, however, it gets exciting when I click on it because I can show the obfuscation route.
And that's where I see my data traffic going through three different cloaking stations and only then to the final destination. It means that my internet service provider does not find out which website I am visiting, the website does not find out my IP address and all the numerous surveillance systems do not find out what I am doing. I can also use it to bypass censorship because my internet provider no longer knows what I want to do. He only sees that I'm communicating with some weird obfuscation node. Actually, it can't censor me and with the help of Tor browser I can avoid both surveillance and censorship.
It doesn't work equally well in all countries. Countries like China do not want their good surveillance and censorship regime to be ruined by a bunch of IT activists. They just block all the obfuscation nodes, however, there are many other tricks in the Tor's bag of tricks that you can use. There are so-called "bridge nodes; that I have to inquire individually from Tor.
With the help of them, I can avoid censorship in a country like China. So that's shortly about Tor browser; usually, you use the Tor browser on a PC. But there are also Apps: for Android smartphones, there is an app with the simple name "Tor Browser", it's a browser app. And there is even an app that helps me to let the complete data traffic of all apps run through Tor; it's called 'Orbot'. And for the iPhone, there is also a recommended Tor-app called 'Onion Browser'.
So this is the first reason why Tor is used. I can access the normal internet anonymously and mostly free of censorship. The second reason is the darknet. That's why we are here today. With darknet, the obfuscation is practically doubled.
As a user of the Tor browser, I stay anonymous. But I know the technical address, the website's IP address. The technical address of the website is not known to darknet either. And it would mean that I cannot access the website. If I want to open a website, I don't know its IP address. It's similar to when I send a letter, but without knowing the recipient's address it won't arrive.
With darknet, this is done using a very old trick, namely a 'dead mailbox'. These dead mailboxes are one of those many nodes that the Tor software selects for me. The dead mailbox is situated between me and darknet address. A friend of mine helped me with a little visualization.
On the one side, it's me, my Tor browser, and on the other hand, it's darknet. The point in the middle is the dead mailbox. It's one of those many nodes. And when I now communicate with a darknet website, I send my information via three nodes to this dead mailbox in the middle and darknet address picks up my information via three own Tor obfuscation nodes from this dead mailbox.
There are several cloaking stations between me and darknet address; thus, we can communicate with others very quickly. I'll show you once more live in the Tor browser what it looks like. This is a website, a mailbox for whistleblower that the Guardian has put on darknet. What for did they do this? We'll talk about it later. First of all, we are interested in this obfuscation route. At the top, there is my Tor browser, below is the darknet address, and here in the middle would be this dead mailbox, which is not visualized here separately.
And I send my data via three Tor nodes to this dead mailbox in the middle; and darknet address picks up the information via its own three Tor nodes. I know my cloaking station; for sure, I don't know the cloaking station of darknet address. So that's the whole secret of this ominous darknet. The point is simply that the IP addresses or technical addresses are hidden, the adresses of both darknet and the users. You can only access darknet address with the Tor browser, with the normal browser you will see an error message. And then you can already guess up that a Darknet address looks a little different compared to a normal address.
It's not 'goethe.de' or 'facebook.com', but a darknet address always ends with '.onion'. What is the onion all about? Tor is called 'Onionroute', frankly speaking, the 'onion navigator'. And that's the principle of several obfuscation stations, or, stated differently, the principle of several mathematical envelopes. This concept is already relatively old, and the inventor said it's a bit like an onion. The onion has a core in the middle, and it has many layers.
And the idea with onion routing was the same. The core is the user's IP address, the user's identity. And to get there, you have to remove various layers of obfuscation, just as if you would have to remove various onion layers to get to the onion core. So the address always ends with '.onion'; thus, darknet address looks a bit strange. This is always a random sequence of characters, either 16 or 56 characters.
The point is that you cannot delete or block a darknet address. That is politically interesting, but it also creates problems, as we shall see later. And at the end a very short question: Who stands behind Tor? Tor is run by a non-governmental organization based in the USA. The web address is torproject.org and you can also download the Tor browser from their website.
You get it for free, and it's neither illegal nor dangerous to use it. Well, at least it's possible to use in most western countries. The Tor project has a good reputation in the world. It is considered the most important opponent of state surveillance.
According to the reputation, it's a mix of Wikipedia, Amnesty International, and maybe the Antifa. However, I would say, the Tor project is a bit contradictory, like darknet itself. Tor was originally developed in a research laboratory of the U.S. Navy in the mid-1990s.
So, it comes from the US military research context, just like the normal internet as well. Then at some point, Tor was released, this non-governmental organization was founded, but the weird thing is that until recently, Tor was financed almost exclusively through funding from the US government. Until recently, around 80-90 percent of the money came from US government sources. In 2017, they finally managed to reduce it a bit.
I took a look at Tor's latest financial report. So in 2017, 51 percent of the money came from US government sources. And the rest from the other sources. And this financial connection leads to numerous mockery, to many questions and conspiracy theories.
It's not good, it's a security problem; so Tor would have to make sure that they somehow become independent organizationally. Still, I think Tor is a clean and safe technology. Although darknet and Tor are not 100 percent anonymous. No technology can guarantee it, but Tor is an open-source which means that the software, the basic instructions are publicly available.
And frankly speaking, people in many countries, especially at the universities, are dealing with the Tor software and see whether there are any security leaks or so called 'back doors'. As I said, despite this weird constellation, Tor is a very safe and clean software. As far as I know, extremely sincere people work there, many people from the German Chaos Computer Club and the international hacker scene. So that's all about Tor. Exactly. I have several follow-up questions. I think it's super interesting that Tor was mostly funded by the US government, around 50 percent of its budget.
But the majority of Tor nodes are in Europe, many in Germany. In northern European countries and particularly in the USA there are not many Tor nodes. How did this happen? First of all, Tor nodes are mostly situated in western constitutional states.
In China, for example, it is not recommended to operate the Tor nodes. You can be visited by the police just because of this. There are a couple of countries - Germany, USA, Netherlands, Great Britain, France. There you have good, relatively cheap IT providers that allow you to operate Tor nodes. People do not take a computer, physically connect it to the Internet and say that it's a Tor node.
They rent a computing space from the major IT providers and turn it into Tor nodes. This creates problems of its own because Tor nodes are clustered within a few large IT providers, especially in Germany and France. That's the reason why there is such a huge concentration of Tor nodes in only few countries. And one can only speculate, why there are so many nodes in Germany. On the one hand, data protection and privacy have a greater cultural value in Germany than in other countries. And also we have in Germany the famous hacker organization Chaos Computer Club.
They also have a very good reputation, and are socially very active. They supported Tor right from the start, and I think they mobilized a lot of resources for Tor. The fact is that in general, the non-commercial digital world has a very strong place in Europe. The USA dominates the commercial digital world with Google and Facebook etc. But the open-source projects and the non-commercial things are located mostly in Europe. Interestingly, often in Germany too.
It's very interesting, thank you very much. The next follow-up question is: How big is darknet today? Is it in any way countable? How many users and nodes do exist, in general? I could show something if you give the possibility to share the screen. This is a statistics portal of the Tor project. They record numbers. Numbers of the onion addresses, of the darknet addresses. They are not entirely accurate, and they are no longer entirely complete.
But they give a rough insight introduction of how huge darknet is; it is almost manageable. The highest number of darknet addresses ever recorded is 200,000. This is an excerpt from this statistics portal.
Some fluctuations always happen, and you don't know exactly what's behind it. It is mostly assumed that it was some botnet, i.e. someone played around with the technology. And the highest number ever recorded users was 200,000, which is very little. The German ending '.de' alone has more than 16 million addresses.
I see. Thank you. So it's not as huge as many people might think. By the way, it's the same with users; Tor has the number of Tor users. And the quantity of users estimated worldwide is around 2 million Tor users every day, which is a very small quantity. Also, you can see the statistics countrywide. In Germany, there are about 182,000 Tor users every day, in Ukraine about 41,000 Tor users.
This are Tor users, and only a small part of them enters to darknet via Tor; The Tor project says they allow a maximum of 3 percent can go to darknet. So, if we have daily 40,000 users in Ukraine, it's only 1200 Ukrainian darknet users every day. With 2 million Tor users worldwide, there are only about 60,000 darknet users worldwide. And that is also very little compared to a site like Facebook. So darknet is very manageable, contrary to what many might think.
Yes, it's true. Perhaps, we can go straight to the second part of our discussion: Darknet and the image of darknet. The media created the image of darknet that it's dealing only with weapons, narcotic drugs, and other criminal things. So I would like to ask the next significant question: "How ethical is it to use darknet? What happens in reality in darknet?" The picture is not wrong per se.
Illegal and nasty things happen on darknet, however, it's a bit more complex. At some point, I thought about how to divide darknet into several different areas. And unlike many journalists, I decided not to use the terms 'legal' or 'illegal'. I noticed that the question 'legal-illegal' doesn't get very far on darknet. Darknet is much more nuanced. And I distinguish between three areas of darknet.
One is the ethical abysses of darknet. That's probably when many people think that on darknet e.g. weapon is being sold. That's one of those offers on a weapons marketplace. The topic of weapons on darknet was once very big in Germany. A few years ago there was a right-wing terrorist attack in Munich.
A young guy murdered other teenagers in a racist bar. And he got his weapon with the help of darknet. Not particularly on such a market place; he got to know his weapon at a forum. But at least it shows that things can go wrong when weapons are traded on darknet. And digital weapons are also traded, cybercrime manuals are traded, botnets are sold, etc.
And the worst use of darknet Is when child pornography is being shared, pictures and videos of children abuse are sold. On this issue, I haven't made a slide. And I think that is nowadays the biggest problem with darknet. Some forums try to shield themselves from darknet and there can be tens of thousands, hundreds of thousands users.
And sometimes the police manage to paralyze such forums. A few years ago there was a great success, especially by the German investigative authorities. There was a forum with the cynical name "Elysium". It had more than hundreds of thousands of registered profiles and, as the Federal Criminal Police Office says, 10,000 images of the abuse of children and teenagers were shared. The forum was run by four men from German-speaking countries. The data center was in a car repair shop somewhere in Hessen.
The people are now in jail, but it usually doesn't take long and the next forum is already online and at some point, it will be just as big or even bigger as the previous one. And that's the huge problem with darknet. You can't currently delete or block darknet addresses.
Even if you know the addresses, and that terrible things are happening there. Occasionally a discussion takes place in the Tor community about whether it's necessary to change the algorithm. Perhaps, it would be possible to introduce some kind of filter system, if 90 percent of the operators of the Tor nodes decide that a particular darknet address has to disappear, then it will be deleted. They didn't make a decision on it yet. Above all, they are afraid that if one day such a filter mechanism is introduced, then maybe the state will come and say, look, you have this nice filter system, so delete drug pages or political pages.
They are afraid that censorship infrastructure will be created through the back door. But I think how the Tor community is handling the issue is a bit irresponsible. We have the attitude, that we take care of the technology, anonymity is a great thing, it helps against surveillance.
And what people, good or bad people, do with it, we can't influence it. That's irresponsible; it is based on the US-American idea that the state should stay out of it as much as possible, and rules should stay out of it too. Somehow you get it by yourself, but when it comes to child pornography there is still no way to react. There is no way and no solution how to deal with the child pornography. This is a huge problem; and both darknet and the Tor community simply have to do their homework. That's right.
And there are no tools or ways, or methods to solve this problem. I mean, anonymity and security on the one side helps Tor users to transmit politically sensitive things, however, on the other side it helps also criminals to provide their stuff. And there is still no way to somehow solve it. They could solve it. One could insert a consensus mechanism. There are Tor node operators, they could decide that certain sites will be deleted.
There is self-regulation in darknet, namely technical regulation. There is a group of the so-called guardians of the Tor network. I think there are 10 people right now. They check the nodes and see whether they are online, whether they behave strangely.
And they can delete Tor nodes. That means, we have a very weird constellation: it is possible to delete Tor nodes if they violate technical rules. But it's not possible to delete darknet addresses if they violate basic humanistic principles.
There is for sure a way to deal with it, however, Tor project currently disclaims all the responsibility. All right, there are problems that we cannot deal with now. But regarding, for example, guns or porn, these are 100% criminal things. You've also talked a lot about drugs on darknet.
There are two sides to this problem - darknet and narcotic drugs. Perhaps, you could mention some details. Yes. The second area of darknet that I would mention,
is its function as a shopping mile for narcotic drugs. And I've made a decision not to claim drugs as an ethical abyss. Many journalists say that in darknet there is an evil darknet, meaning narcotic drugs, terror, and child pornography. As for me, if someone smokes a joint that they bought on darknet, it is not ethically the same as consuming pictures of abused children. I think these are completely different categories, and that's why I put it an an extra area - darknet as a shopping mall for drugs.
That's what a lot of younger people know about darknet. It has become very popular because there are series about drug trafficking on darknet, and there are also large marketplaces. I'll show one of those, it's the former market square. I'm not showing you the current ones, as I don't want to advertise active markets.
For example, 'Empire Market'. This is another market, 'Berlusconi Market'. These are marketplaces, where various goods are traded, but first of all the usual intoxicants - cannabis, cocaine, ecstasy. At first glance, it is such a completely strange world, but at second glance it shows that it somehow seems familiar to you.
They imitate normal e-commerce as we know it from Amazon or eBay. They basically work the same way. You have marketplace operators who receive commission, you have traders who compete with each other, and you have buyers. You have also a product policy, so the worst things are forbidden there. Child pornography is completely taboo.
These are two completely separate worlds. You trade with cryptocurrency. A long time ago it was Bitcoin, now it has been noticed that the police can partly crack Bitcoin. So, now we have other cryptocurrencies. The goods are sent by regular post. For example, in Germany with the 'Deutsche Post'. Many consumers have it sent to their normal address.
It is rather unlikely that the dealer will keep the list of buyers that later can be found by the police. And even if so, the prosecutor won't be interested in an occasional junkie. That is not entirely wrong, but it can still happen that the police knocks at your door at 6 a.m. And this trade works amazingly well. The most important feature is user ratings. Let's imagine, a student from Kyiv orders 10 ecstasy pills or an investment banker from Frankfurt orders 5 grams of cocaine on darknet.
Then you will be asked to write a review. The rating could be "Great stuff, I'll be back." or it could be "Keep your hands off! It's a scam!" With this user revue rating, it is possible to create a little bit of trust even in darknet. Large traders who want to stay in business won't scam their buyers, as they will get a negative rating, and no one will ever buy anything from them. This is going surprisingly well, and, perhaps, it can frighten someone. However, I was surprised as I noticed that there is an astonishingly differentiated view in the drug-related research.
You see risks, but you also see opportunities. The risks are clear. On darknet, it is much easier to get narcotic drugs of all types and amounts.
This also applies to children, teenagers, and mentally unstable people. However, on the other hand, social opportunities are being discussed. Can you imagine that? This is based on the fact that drug-related research has slightly changed its line.
It is no longer a question of considering how the state can ensure that people don't use illegal drugs. In the last decades, it has been shown that it just doesn't work. No matter how much the state can tighten the laws, people just continue to consume illegal narcotics, that's why addiction-related research did change. The following question would be more exciting: "How to effect on drug consumption, so that people get as little harm as possible?" And if you look at the darknet drug market from this perspective, you can clearly see the opportunities. On one hand, you no longer need to go to a dealer's apartment or the park and maybe got turned around the finger, you simply buy the stuff comfortably on the Internet.
So, it's safer to get the narcotics, and there is quality control via the user reviews. The problem of lack of quality control in drug dealing can turn out to be very difficult. It happens again and again that people after consuming harmless amounts of mostly harmless narcotics have to go to a hospital because the drugs were tainted or diluted. Consequently, tainted narcotics are much more dangerous than the narcotics themselves.
And, some cities provide now and then different model projects. In Berlin, for example, there is a checkpoint, where people can come with their drugs; they are scanned and you get the information what's inside. However, normally you don't have quality control. While the users' reviews provide a reasonably functioning model of how a consumer can in a way reduce the harm and the dangers. I think it's a very exciting discussion.
I know, however, that this won't resolve all concerns about this phenomenon. Fortunately, I can still add something regarding the illegal things on darknet. And one thing is that darknet doesn't have a monopoly on cybercrime. Everything illegal, either drugs, weapons, child pornography, terror, or Nazi propaganda, is also handled through normal channels. That canwould be handled via e-mail, via WhatsApp and Telegram Messenger, via normal websites. Besides, darknet is rather small.
And I would presume that more drugs are traded via closed Facebook groups compared to darknet as Facebook simply has a thousandfold more users than the relatively tiny darknet. Also, it might be mentioned that darknet is not a legal vacuum. It is more difficult for the police to investigate technically in darknet, but they are still very successful.
I once put together a small Hall of Fame. That was AlphaBay. When I wrote my book, it was like the Amazon of darknet. I thought it would exist for years or decades. I even conducted an e-mail interview with the CEO that I planned to include in my book.
However, once the book was almost printing, it was announced that AlphaBay was closed. If you visit this page today, it looks like this. Whenever the police close an illegal darknet site, they make a banner to show that they were here.
'Hansa Market' was also on darknet. That went offline at the same time as AlphaBay. It was a concentrated activity of American and Dutch investigators. Today it looks like this. Once there was also Wall Street Market.
It would go through the press for about 2-3 years, and nowadays it looks like this. So you can see that the German authorities are technically not as ambitious as the Americans. Every illegal larger darknet site will be paralyzed at some point. It's technically difficult to investigate, but the police use undercover agents.
They buy drugs, guns, and usually, some mistakes happen. Always whenever goods are physically being sent back and forth, there is simply a point of connection between the digital and analog world, because the things are sent to a postbox or delivered in another way. It's more complicated when you send back and forth only bits and bytes.
Especially on those horrible child porn forums. The police are actually dependent on the operators that make very gross mistakes, or hope on technical luck finding some security leaks in the software. The big players from these marketplaces end up in jail at some point.
It's very good to know. There is really a lot of hope. But we definitely can't talk only about this negative side of darknet. Darknet is relatively small; it was created with a completely different goal, a political goal. So that one can bypass the state surveillance. So that political activists in such countries as e.g. China and others,
countries with a strong political regime could upload and send their secret data there. Yes, that's right. There are political parts of darknet. The Tor software was not developed for dissidents, but it has an official explanation: It was developed by a mathematician in a research laboratory of the US Navy. And he reasoned that it could be very exciting for the American government, military, and intelligence activities, if they can do something abroad not showing their identity. The original benefits of darknet and Tor technology were for sure not positive.
Or depending on whether you find it positive or negative. So the origin was a bit more complex, but in the meantime, many people believe darknet to be a great dissident space. Also, I speculated if and in what way darknet is a political arena. It was a bit frustrated at the beginning, as I found very little. I discovered few things that had a small reference to politics. I was a little frustrated because I didn't discover the following.
I thought, like perhaps many other people, that darknet has numerous darknet-exclusive content. Perhaps hundreds of blogs from opposition members from China or Saudi Arabia that are only available on darknet and nowhere else. However, it's not the case. If you find interesting political content on darknet, then it quickly turns out that it's the same content one can find on usual Internet; and it was just copied into darknet. There is a very small darknet society, there are some discussion forums that are sometimes very exciting, which have to deal with illegal things. But frankly speaking, you almost don't have a specific darknet society. What I find exciting: various programs use darknet, but they don't provide web content, they are rather a kind of program building block.
For example, "Onion Share". This is a program for PC. It was developed by investigative US-journalists after the Snowden revelations. It works the following way: I load the program on my computer, I start it, and then I can share files. I put into the program an explosive document, and then the program itself generates a darknet address.
That means I am the owner of a darknet address for a short time. I provide this address to the recipient, who then can call up this darknet address with the Tor browser and download the document directly from my computer via a darknet address. It's very exciting, it makes surveillance extremely difficult. Usually, you share documents via e-mail or Dropbox or wetransfer, or whatever the service is called.
There is always a company in the middle, that sees who is communicating with whom and can even look into the documents. And with Onion Share, the entire communication is simply encrypted and nobody external can see who is communicating with whom, because everything runs over darknet. There is also a darknet messenger called 'Briar' for Android. I communicate directly from darknet address on my Android smartphone with darknet address on the other person's smartphone.
And there is no database in the middle that can somehow find out who is communicating with whom. This is such an exciting political use of darknet. Also, another thing surprised me a bit. However, I find it the most relevant. Darknet is a kind of a secret door to the normal Internet. Different websites are presented on darknet; there they make their entire content or certain functions available.
Various media, for example, the New York Times, has a darknet address. It looks like this. And there you can read the normal content of the New York Times. Deutsche Welle and BBC also have such a darknet appearance.
Funnily enough, Facebook has that too, as does the CIA. And why are they doing this, the New York Times, Deutsche Welle, and Facebook? They say that they do this for the people that anyway have to visit us via the Tor browser because our normal sites are censored in those countries. So when you put it on darknet, then it works a little faster and more elegantly.
The benefits of this are somehow manageable. I think that's more of an intention to show that you are avant-garde and that you are interested in freedom of thought. Besides, the TAZ does it too. TAZ is a left-oriented German daily newspaper. Furthermore, I found out something very exciting.
The most important left IT communities also are present on darknet. Different editions of the global media platform IndyMedia and different IT communities are presented on darknet. For example, there is an IT community called RiseUp. They offer communication tools for human rights activists that are particularly secure against eavesdropping: E-mail services, text programs, where you can simultaneously work on texts via the Internet.
You can find them on the normal Internet at RiseUp.net, but they have set up a separate darknet address for each of their tools. Also, there is such a group from Berlin called 'Systemly'. I once asked Systemly and the German office of IndyMedia why they are doing this. There answers were very similar. They said they had been instructing their users for years: "Guys, use a gate browser. We do not collect any data of yours,
but we don't know what happens between your device and our website, whether it is recorded that you are opening a left media project or whether data is being manipulated. You are much safer with a Tor browser." That's why they said that darknet was a logical consequence for them, and my impression is that it's an educational measure. They want to convince their users to use the Tor browser, which is why they also offer their content on darknet because darknet can only be used with the Tor browser. I find that very exciting, and these are the most important left-wing IT communities who have discovered darknet for themselves, although they didn't want to tell me how many people use it. I think it's still manageable.
Besides, there is another political use of darknet, which I find the most exciting at the moment. The media I mentioned previously placed their entire content on darknet; also there are various media that build up something like a darknet for whistleblowers. Various media started after the Snowden revelations to put up on darknet mailboxes for whistleblowers, for such people like Edward Snowden, who work in the authorities, in the secret service, in large companies. There they get to know about some odd things happening, and they want to make the information available and to transmit some explosive documents to the media. That's a nice thing, but it can be relatively dangerous.
So the media set up contact points for whistleblowers. And some of these media have also placed these mailboxes directly on darknet. A lot of media do that, I would say 70-80%, and there are many very big ones among them. The New York Times has a darknet mailbox. The Guardian, the IP news agency, the VICE magazine.
In Germany the Spiegel, the TAZ, the IT publisher Heise and the Sueddeutsche Zeitung. They all have a darknet mailbox. You go there as a whistleblower, upload a document, and then the New York Times or the TAZ gets it. Besides, there is also another model: Media from one language area, actually competing media, have come together.
And together they provide such a mailbox. Such as, for example, Source Sure. The French daily newspaper Le Monde is there, along with the Belgian daily La Libre and the French-speaking Swiss radio. And being a whistleblower, you go to the mailbox, upload a document, and then you can specify who should receive this document.
I'll show you such a mailbox for a moment. We had a quick look at it beforehand when I spoke about how a darknet address looks like. There are always two functions. If I'm a whistleblower, I'll click on this field on the left.
Then I see a secret code, a kind of password, which I write on a piece of paper, then I go on, and send the document to the editorial office, and I can also leave a comment. After the editorial team receives it they can decide to communicate with me again. And that's what this secret code was for. So as a whistleblower I come back a few days later, enter this secret code, and then the editorial team can communicate with me.
As for me, darknet mailboxes are the most exciting political use of darknet that has a certain social input. When whistleblowers make social scandals public, that's a fine thing. And that's where we get socially ahead. With these darknet mailboxes, the editorial offices can ensure that the whistleblowers are on the safe side.
That is what I would understand as a political darknet. This political darknet does exist, but everything is still relatively manageable. I also didn't find out how intensively these mailboxes are being used. But the media that run them are at least proud of it, and they usually consider that it makes sense for them. Thank you very much, Stefan. Perhaps, the last question. We talked a lot today about Tor Browser and Tor in general.
Is there any other alternative to how you can surf darknet without using the Tor Browser? Perhaps, there is something else? You can theoretically enable other browsers to run through Tor. And there is also a browser called Brave, which has the Tor functionality, and the Firefox browser is also thinking about somehow providing the Tor function. However, they are afraid that if they offer Tor, they will completely crash the Tor network because then suddenly tens of millions of users will use Tor.
If you recollect other anonymization technologies, there are definitely other darknets. The English-language Wikipedia article says there are in total 12 darknets. Most of them can only be understood and used after studying computer science for at least two years. Two darknets are somehow interesting – I2P and Freenet.
They have a certain dynamic in terms of content. They are even more radical than the darknet. Darknet divides between normal users and infrastructure providers. While with I2P and Freenet, as soon as I participate there, I'm both a user, and at the same time an infrastructure.
It means, I get data that are determined for me and also pass on the data of other users. And that's even more exciting. But the Tor darknet is simply much larger and dominates public perception. On Tor darknet much more is going on. It's interesting how such a result was achieved. I always wondered why Tor darknet prevailed among others And somehow I kept concluding that it had something to do with the financing.
The Tor project had a budget of 3 or 4 billion US dollars each year. So developers can be paid, they get market-based salaries, hundreds of thousands of dollars a year. However, other projects are more or less voluntary technology projects.
Tor can do a lot more, it can provide the core function. They have people who can check out the technology so that normal people, nonprofessionals can understand it. They have people who can travel around the world and speak at International hacker conferences, and promote the Tor community, while others cannot afford this.
There are other exciting anonymization projects, there was or is still a German anonymization project - JAVA Anom Proxy. It is now called Jononym, but it didn't make its way through. Primarily, it was a university project, then they made few mistakes, and now almost nobody uses it anymore.
So, unfortunately, Tor is the best and the most important anonymization project, but definitely there are also alternatives. Thank you very much. So we mention again the US funding issue of Tor. It's important to know and to understand why Tor became so huge, relatively huge. Thank you, Stefan, for this very exciting discussion and presentation. I think everyone has understood that Tor, and darknet, and everything that goes with it, is a very complex subject.
And there is no clear "yes" or "no", no black or white side. We highlighted a small aspect of this issue today. The recording of our discussion will be available on the DATA CTRL Center's online website, as well as on the Goethe Institute Ukraine website. Our discussion will be also subtitled in English.
Stefan, thank you very much for your expert view, I wish you a nice day. Yes, thank you for the invitation. Goodbye. Goodbye.
2021-03-05 10:01


