Hack the Institution – A Map To a Strong Partner-Based Security Program
- [Molly] Good morning. - [Bobbie] I have to say, we have a larger crowd than I had expected for 8:30 on a Tuesday morning after our first night in conference. So thank you all the early risers for appearing for what I hope will be a fun 45 minutes. My name is Bobbie Stempfley.
I am the business unit security officer at Dell Technologies, focused on the product organizations at Dell. And my compatriot here. - [Molly] I'm Molly Mae Potter, caveat to this as I am no longer with Dell. So today we're going to talk about the partnership and the experience that we had while I was working at Dell, but I did want to go ahead and put that disclaimer out there as we go through this. - [Bobbie] We have the standard disclaimer related activities.
I just want to assure you that with luck, you're gonna come out of the next 40 or so minutes understanding what we have done at Dell in the creation of business units, security, teams and activities, the shared responsibility that, that has between the central security organization and the business units themselves. Hopefully we will give you a couple of warnings of things that have not gone well. In Dell land, I said I support all of the product business units. Molly's experience had been in the client side, so just one of the product units that's there. So we're gonna talk about what didn't go well, what bumps and bruises that we accomplished across the way, and hopefully leave you with some interesting tidbits to take back home with you. And with luck, we'll have time for a few questions at the end.
The one piece of housekeeping that Steven reminds me of is if you do have a question, please come to one of the mics. Don't shout it from your seat. That way the entire audience can hear the question there. Let's see. Molly, anything else we... - [Molly] Yeah, so we are going to really talk about our journey building this together. So as Bobbie said, she came from...
She is in the security side of the Dell house. I came into the story not a security person, really business operations, chief of staff, digitalization, transformations. And so this was our journey together diving right in to building something brand new together. And that's how we're going to put this together.
So it is just our experiences going through this. By the time I had left Dell, the other organizations across Dell had started also building these partnerships. And we'll talk a little bit too about some of the other models that had been formed within the Dell organization in construct and the pros and cons to those as well. So again, open discussion as we go through this today.
And I'm looking forward also to hearing a little bit about some of your experiences as well going through building partner organizations with the business. - [Bobbie] And if we're ready, we're gonna get started. So just as a reality setting, remember we've been kind of busy in the security industry over the last, I don't know, two or three years between the growth of ransomware, targets against supply chain, threats against supply chain, and physical constraints in supply capabilities, as well as a range of issues at Dell in terms of changes in the business construct and the organization in that space. It became pretty clear several years ago that we needed to continue to dig security into the business units, that we needed to not just have a central security organization, but as it matured, we needed to have deeper relationships from the ground up in each of the business units. And that's where we really started to analyze and understand what was necessary.
One of the first steps within that was an important role in terms of governance. - [Molly] Yep, so at this point in time, our security engineering SMEs were really taking the brunt of the hit for all the security responsibility within the business. So one of the lessons learned after an incident response was, hey, we need to build a governance team.
That was part of the action item that came out of it. As we're going through this, they said, well, who are we going to go ahead and lead a security operations team to really work with the BUSO, put a strategy together, and to be a central management hub for the business unit? And at that point in time, I was running business operations, doing a lot of budgeting, headcount, digitalization, transformation work, and I was ready for something new. And I found out from my boss that they were looking to put something like this together.
I said, hey, I'm really interested in doing this, and they said, well, we don't think this is going to work. You're not a security person. I don't know who's gonna bite off on this.
I was like, well, let's just give it a go. My background was also I came from the Air Force and Air Force Acquisitions. At that point in time, the executive order publication had also come out. - [Bobbie] Yep. - [Molly] And our executive said, what is this? - [Bobbie] So I wanna point out a couple of things if you haven't noticed, and that's one of the first things we had to work on was language, right? Security operations and operations at Dell are different things, right? Business operations is how the business runs, right? What's the systems, tools, processes, data that occurs. And when we talk about security operations in the security field, we think about security operations centers, monitoring and response.
And so Molly and I worked early in the game to understand each other's language and make translations as a part of it. So as we built on our strong product security program, because we have a strong product security program focused on our hardware and software products. The executive order came out and now we had to think about things at a systemic level in a way that we had the pieces for, but hadn't stitched them together in business operations in order to be able to tell a cohesive security story. And it became really the pivotal point. And I think the refining moment for Molly's team here was to be able to stitch together all of the business elements with the security elements into a cohesive story around how Dell was responding to the Biden executive order on cybersecurity.
Remember, this was about deep information about your security development processes. It was about software bills and materials. It was the zero trust journey. It was a whole range of very important security elements that we needed the business to deeply embrace. And leveraging her team, we were able to do that.
- [Molly] And at that same point in time, coming from business operations, I understood how money flowed within the business, how investment decisions were made. And so it was also a pivotal point for me to go ahead and put together a strategy and an investment plan. And to be able to really socialize it, I had all of the right level of relationships, deep relationships with the executive teams across product marketing, across engineering, across operations. And so while Bobbie was new to Dell at that time, I had years of experience with deep relationships within the business. So while I was relying on Bobbie to make sure that we were building a strategy that was sound and where we needed to go from a north star perspective with security, I was also able to help her inculcate this into the business and influence the investment strategy to get this team up and running. So that was also a very important part of how this shot clock actually was executed.
- Yeah, and I think as the continuing crisis occurred, right, as we had the Russia-Ukraine crisis, as we've seen the shifting trade environments and as we've really been maturing as an industry into better data governance, I think what you're gonna see over the next several slides is that we've developed a model that works really well for this particular use case, I think. - [Molly] And I think once the... I think this is when we knew it started working was when we had the Russia-Ukraine crisis and the greater momentum and shifting regulatory trends, we now had a team in place within the business to be more proactive than reactive. So this was our first sign that people were in place to do this full-time, not part-time, to do this well and to be able to see things through.
So this is where our journey really started. - [Bobbie] Exactly. And we are a converged security organization. So we have the span of security responsibilities, not just the cybersecurity responsibilities. So product security, cybersecurity, physical security, enterprise resilience, and personnel issues.
So what does this mean, right? This isn't an... This is an integrated operational function, but we are... We have a level of accountability that's shared, which is an unusual model at Dell there, but I think a necessary one because we both bring vital information together. So from the business unit security construct, right? I bring to the table corporate security enterprise risk conversations, right? I am the voice of what is the necessary security north star, what are the vital risk issues that need to be identified.
I'm focused exclusively on protection of the Dell brand against those spaces, and work hard to set meaningful, appropriate security goals that are business-aware and necessary and executable. Molly on the business side. - [Molly] So I took this and I aligned this with the business priorities and our customer needs, right? So how are we actually going to be able to map this to our product story, to our customer demands, and also to be able to differentiate? Also, how do we start looking at security as a success for our products, for our customers, but also making sure that we are doing the right thing internally within the business to secure Dell? And that's where we started with those foundations. And how do we start measuring security transformation success within the business in business-level discussions? How do we also start shifting security discussions left when we start talking about new programs, about new investments and the roadmap, and to keep that on base and to continue to keep going. So this was a really amazing opportunity for us to not just put words to paper, but really actually be able to proactively execute this across the business. And again, at this point in time, I was also supporting all the different product groups across the client solutions group.
There's multiple product groups there. So we were also starting to drive a lot more efficiency and to make sure that we weren't repeating work in different business units as well. And so this also became a business optimization priority as well in how we were able to make sure that we were doing this together, we were doing it in an optimized way and the business was driving along the same trend track. - [Bobbie] Yeah, I think what was key here, and I would argue has been key every time we've tried to do one of these things, is to start recognizing what are the governance and business operations functions that the business runs with, right? So it isn't about thinking about what's best practice in security governance, that is necessary, absolutely. But understanding what's best practice in business operations and inculcating the security conversation into that discussion.
Because at the end of the day, when a business leader is having to make the trade, right, they don't want the security information over here and trying to make it absent the business information. And so we had a couple of options here. We we could have created a set of security governance activities and tried to bring business effort into it.
That I think is a failed strategy in many instances. But that meant I had to spend a lot of time learning the business language, right? That's the piece that that's really, really important and a big part of my job is translation. So in terms of the things that we do together, right? That shared accountability function, which again makes people, myself included, a little uncomfortable. We have a responsibility for the workforce, right? We have a shared responsibility to understand what security information everyone in the workforce needs, and which added security in insight and information the security professionals in the workforce, whether you be product engineer working on security features, you be a security champion, an extension of our SDL programs into the product teams, or whether you be a sales individual who needs to understand how to avoid fraud in your sales interactions, that's a shared responsibility that's there. In the focus on the mission, I think the shared responsibility there is really the negotiation over priorities and program activities in that space.
And there's a fair amount of arguing that's necessary in order for that to occur, right? How good is good, how much is necessary? And the ability to translate the security outcomes into business metrics. And then on goal setting, Molly, why don't you pick that one up? - [Molly] Yeah, so on goal setting, it was really focusing on simplifying. Whenever we brought up the word just security, people just started backing away, right? So how do we make this easier for team members to get access to resources, to understand in a very simple language what it means to them, why it matters and what our priorities are because it was all over the place. And so together we worked very hard on making sure we had a centralized vision and we also had a centralized messaging, centralized communications and resources. That was huge for us. And that was a really great first step so that whenever questions arose, there was someone within the business and there was also someone within the SRO and security organization to work with the business.
So it all funneled through centralized and simple channels, which didn't exist before. And I think the other thing was distinguishing R&R. So understanding what came from what person's calendar.
If it was going to be more enterprise and strategic, Bobbie had the big role and responsibility there. If it was business and operational and it had something to do with a business KPI or funding or personnel even within the business, it came from my calendar. And that also really helped distinguish very quickly who went to what function. But at the same point in time, we talk on a daily basis. So making sure that there was transparency on both sides on the background of where asks were coming from and why, and the potential red flags ahead of time that we needed to watch out for. That way we could proactively work together to execute our mission.
- [Bobbie] And identify areas of both commonality inside this particular business unit, but across the business units as a whole. And I think that really helped, right, in terms of our quick wins there. Now it required building combined teams.
And those combined teams, I think in any organization, the first few hires you make in a team can be really, really impactful. And if you get them right, it's great. And if you don't get them right, you suffer from it for a while.
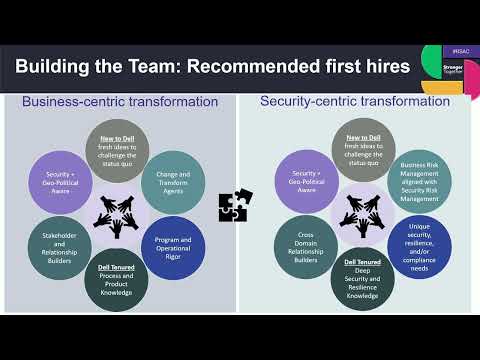
So let's talk about the first few hires and the kinds of skills that are necessary. - [Molly] So I went about this a different way. As soon as my organization at that time had been funded, I started getting tons of resumes and most of them were from security SMEs or security engineers within the organization. And I thought, well, if we're doing that, we already have security engineers within the organization and they do an amazing job at delivering secure products within our business, but they're not great program managers.
They're not always great at strategy and they don't always see the bigger picture and work cross-functionally. And I also want some new blood. I want people that think a little bit differently.
So I went and I really hired program managers. So when I formed this team, in another way I kind of differentiated this as I said, I'm not a security organization. We are a transformational PMO focused in security transformation in modernization, optimizing and driving a mission.
Aha, it clicked. So now I'm looking for transformation PMOs and program managers. I'm looking for people that really know the business. I'm also looking for people that have come from different businesses outside of the compute world.
And so I hired half new to Dell, half legacy Dell, folks that had really deep relationships across the business. I hired people that were geopolitically aware, very curious, and also came from a very variety of backgrounds. Some of them had security experience, some of them didn't. I also knew that I really wanted to make sure that the organization was going to modernize and transform with the business itself. So I also hired team members at that time that were also very digitally savvy in data and also digitalization, because I knew that when we wanted to go forward on this, we wanted to go faster and when I wanted to hit some of those points that had caused issues.
And so bringing in this new team was very different and they were very new working together. But we went through the forming, norming, performing stages really, really fast. And so within only a few months of the investment, we had a fully functional operational transformation PMO to go and drive the priorities with the business. - [Bobbie] And I think the key to that is the transformation component that's there, right? I was able to leverage the idea that we needed to transform how we operated segments of the business there. My team is deep security expertise, right? I have enterprise risk management, cybersecurity and product security expertise on the team so that we can do first stop response activities so that we come with the credibility to the business about what's necessary and what's there. Now, there's a couple of unicorns that we had to defined because I needed that deep security expertise and deep relationship building, right? One of the things that I think we all know and we say, but I cannot say it enough, relationships lubricate every action in security.
Right? All we do is put friction in the system most days. And if you don't have the relationship in place now and going forward, that friction just gets harder and grinds the gears down more and more. And so you really have to have a focus on having people with the right skills to do that, but making the time to do that as well.
And so as we were really thinking about what my team needed to look like and what kinds of things I needed to hold them accountable for, I actually hold them accountable in their performance plan for a relationship. And we talk about what are the measures of valuable durability in those relationships that are there. So you see cross domain relationship builders on there. I can't sort of foot stomp that one, I think, enough. And like Molly, understanding, having a combined team of people with deep understanding of the Dell culture and the Dell organization and some new blood in place was really important, important for the activities.
But the security expertise exists in the business unit security officer here in this model. Okay, so once we got past the first hires, what was important? - [Molly] So I started with communications. A lot of it was if I was gonna build a strategy and figure out what was really needed, I needed to hear people out. So I really became a therapist, I felt like, for a lot of the security SMEs in the organization. What have you been missing? Where do you think we need to go? If you were given a million dollars by the organization tomorrow, what would you do with it? What would make your life easier? What would release your burden? What do you think would make the organization move faster? And I listened.
And within those communications, we put together the strategy. Once we had formed the team, I went on a roadshow. I probably sounded like a used salesperson, but I wanted to make sure that every single organization that I was responsible for supporting knew that we existed, why we existed, that we were there to support them. And so I spent about two months burning the candle at both ends doing global staff tours.
And that opened up a whole new world. I started finding out new things about the business that had maybe been buried and they came to light and now they had a place to go. And so centralizing those communications was key.
We also started putting together newsletters to help educate and inform our team members about the fundamentals of security, making security accessible and kind of a one team success knowledge transfer, right? That this isn't just a few people that are experts in security, everyone can be an expert in security within your field. This is how we pulled this together. And those communications really started driving momentum in our success with relationships and also getting security earlier into programmatic discussions much faster.
- [Bobbie] Yeah, and what was really important in this interaction is I had the security content, right? I knew what needed to be done, what the messages were that needed to get across. I had a business space for them, right? So we had a shared face in that space, and I think we certainly have the kind of support all the way up to senior levels in the company, but it enabled that first knock on the door when I showed up to be a much softer knock because it had a business face in that interaction. And so when we took all of this information from the listening and communication, and really brought it to the table with the kinds of compliance and policy information that was necessary, we were able to identify miscues between the two situations.
Places where the way the policy was written was just inflaming even though everyone agreed on the objective, right? And that became a really important point for us where it was the global policy is X, absolutely, but we know that there are use cases, whether it be how we do software development or customer capture kinds of activities where this policy in the way it's worded just automatically turns the ears off of the people who are the recipients of it and now we have a fight. We didn't need that fight. We picked it and we didn't need it. So we changed the way we aligned that action and set global policies in language that was understandable by each of each of the business partners in that situation. And that let us go to KPIs and a set of operational rigor that rolled this out through all of the business meetings where decisions are made, through all of the engineering functions that were there. Again, sliding it into the process that the business already had.
You wanna pick up on that? - [Molly] Yeah. So the operational rigor was a piece that I think we were able to actually inculcate through the rest of SRO as well. We started forming best business practices for how security information needed to get to us within the business and how business information needed to flow back to the SRO perspective as well.
And even though it was a little bit of a rocky road, it ended up setting up the momentum for us to help other business units across Dell find best practices to work and share information. We started standardizing some of the things that our executives would see in reviews, right? Simple things like that. Making sure that security messaging wasn't 50 slides long, but five slides. These are the five slides you're gonna see and these are the five things that we need every single time. And then the other thing I think behind that as well, the operational rigor was the BMS, right? So the business management system is what we called it, to make sure that our executives got that normal tick-tock, right? That security wasn't something that you heard about, that you got a review when there was a dumpster fire going down the river, but it was something that you were proactively hearing about.
And it also helped make the investment decisions and also talent decisions and other business priority decisions related to security forefront and not just a last minute thing. And I think that that really started helping us gain momentum from the top as well, just through the operational rigor of sticking to these key things over and over again, but also holding our business partners accountable for sticking to those standards. - [Bobbie] And that's that comment I made earlier about relationships getting alignment between the business, what business risks the business is tracking, how the security risks align with those business risks, understanding how far, how much progress we are jointly agreeing to in order to align that activity is a really time-consuming, sometimes difficult, but very necessary set of conversations with a big S, right? It doesn't happen in a single meeting. It doesn't happen with a single presentation.
It happens again and again and again. And we need to re... Well, one of the things that was in our business management system was to revisit those commitments on a very regular basis, reminding people this was what we committed to, this is what we agreed to. Maybe there's some set of circumstances, business or external, that is necessary for us to re-baseline on. But we constantly were coming back to the presidents and the senior vice presidents inside the business unit and saying this is what it looks like, this is the KPIs we agreed to, this is where we are, this is where we need to renegotiate.
And we've been crystal clear in that partner alignment about who is responsible for accepting what security risk, right? That clarity of roles and responsibilities. I know, again, these are things we've say, but that clarity of roles and responsibilities and that accountability for business risk and security risk as an element of that is incredibly important and cannot be said at a macro level. You have to break it down into specific issues, and say for this issue, the business gets 51% of the vote, for this issue, the security team gets 51% of the vote. And sometimes you learn that as you go along. But that became another foundation for us in sort of the final activity in terms of strategy setting, because we have a...
I have a shared business and security strategy within this business unit. And, Molly, why don't you talk about the work we did in getting that. - [Molly] Yeah, so this was actually... This past year was the first year that we actually built priorities and strategy from the ground up together. Imagine that.
To make sure that we had the funding and the resources aligned, that we were committed to the same priorities above the line and that they weren't always going to be the same for every business unit, that we had to right size it for the business, and we also had to right size it from an enterprise risk perspective as well. And so that was maybe a four or five-month negotiation back and forth between budgeting, between resourcing behind a shifting world in security and regulatory. This was something that we started, yeah, four or five months before we made the final decisions, started doing executive alignments where we're red, yellow, and green on where we need those commitments. And so from the talk down from a business priority, we started having those conversations. So by the time we entered the new fiscal year, we were both aligned on this is what we're committed to this year.
Not only from a larger transformation and programmatic perspective, but what those specific goals were that we were going to accomplish as a team together. Not only from a security organization owning them, but also from a business perspective and what we were going to meet. It wasn't always perfect from both sides of what we wanted, but we knew they were both accomplished or we could both accomplish them with the resources that we had, with the priorities in place, and that we also could build a plan for the year proactively to meet those goals. And with that being said, it also helped the security team start working much more efficiently, much faster on their goals.
And that we weren't still halfway through the year going, well, I didn't commit to this. Well, I didn't commit to this. Why am I red? No, I'm really green, which had been the years previous. And then on top of that, we also now had program managers to help hold each side accountable from both sides, right? To give those progress updates, to understand the nuances. We knew that we still had the right to change our mind. That's just business, things shift.
But we now had requirements that had been aligned where we knew where those shifts were gonna happen and change management to those requirements. So now you're starting to see the operational rigor play out, the communications play out and that the priority setting, the expectation management kept staying aligned. - [Bobbie] Yeah.
One of the really difficult things during this period of time is that different business units have different planning cycles. And so my planning cycle in the security organization was completely out of alignment with the planning cycle in this particular business unit with the planning cycle in other business units. And so we really needed to understand from a security standpoint, what were those business planning cycles? So lesson number one, I think I learned 25 years ago, follow the money, right? What organizations fund is the strongest representation of what they think is important. And so really understanding what the budgeting and AOP development process was for each of the different business units was I think an important lesson for us going forward. So having said these as wins, we had a couple of things that sort of were important for us to move forward.
And I think we've covered a bunch of these, but let's highlight a couple here. Let's see. We've talked a lot about communication and shared communication, incredibly important. We've talked about the iterative priority alignment that I think, again, really necessary.
Executive accountability and where shared accountability is necessary, I think is also one of the key items that are there. The other thing though, is it's particularly easy in when you're growing a relationship with a business unit for everything in the news to end up as something that lands in the security team's desk with, hey, what are we doing about this? Or, hey, I just talked to executive Y and they are worried about problem Z and what are we doing about this, right? So you really have to guard from the beginning from becoming the catch all here, right? Keep focused, hyper focused on the things you wanna make progress on and priorities on. And so what's the balance between relationship building and credibility building with just taking on everything, and therefore not being able to be successful? So that was some of our early wins. You wanna talk about the momentum? - [Molly] Yeah, I think one of the biggest things that we kind of haven't hit on yet is cross-functional mentoring.
So the unicorns that Bobbie found mentor the unicorns that I found and vice versa, right? So those that are really deep and have established relationships within the business and understand all of those business processes now were getting mentored by those with deep security knowledge. And the deep security knowledge that may be newer to Dell or newer to the business, now we're learning all the business products, our business products, processes, and understanding how we got things done within the business, right? And I think that was one of the biggest ways in which we got momentum. So now we had advocates within the security organization that while we weren't represented, understood how the business was working. And also when we have those that were on my team specifically that were my lead transformation program managers or operational engineering leads, they understood the security imperatives as well.
One of my team members at that time was also in Taiwan, really strong program manager, had a lot of pool there, very established within the program management community. She now started showing up to all the core team meetings and also all the development management meetings and being the security representative to make sure that security was talked about within our development processes. That hadn't happened before, all because she had been mentored by one of her unicorns who had the deep security knowledge that we were looking for, and they talked to each other almost on a daily basis. And so now you start seeing even partnerships at a really working level taking flight. - [Bobbie] Yeah, and you'd think from what we said, that all of this was easy, but we got a bunch of things wrong as we went along.
And it's always helpful to sort of start there. And one of the things that we got wrong was back to the comment about the budget processes being different, we really did not understand each other's business management systems, right? We didn't understand the processes by which the business makes decision or the security organization makes decisions, the escalation paths and the items that were there. And that ouch hurt quite a bit early in the game there as well. And so taking the time early in your relationship, early in your interaction to really understand what the incentive structures and those drivers are is really important.
- I think another big ouch was we had security engineers that were really incredible subject matter experts within the development process. And when we had incidences where we needed to do something rapidly, we heavily relied on them to get things done and realized they weren't the best program managers. They're not the ones that should be doing executive communications. They're the ones where you get the right answer from them and you know the so what impact. And they're going to go and do the right thing to make sure it's fixed, but not relying on them to then just take that forward and make sure that all the ends are tightened up as well.
And that's part of the reason why I did end up hiring primarily transformational program managers. Another one was assuming a one-size fits all toolbox. As we started building solutions and building modernization programs within the security space, we thought, okay, well, we're doing this for client solutions group. It has multiple product groups.
Products are very different. The customers are very different. And so even if there is one program that we're driving, usually there's four or five different work streams that have to align to different areas of the business with that. And that's a lot of different requirements, a lot of different stakeholder setting and also different timelines. So it becomes a lot more complicated.
It's not just we're going to go roll out this one new security transformation effort. It's okay, we've got to go align this and meet the business where they're at, meet the products where they're at, and understand each individual different customer requirement with where they're at as well. So it becomes a very complicated program management effort. This is not simple.
And so whenever we would give updates to our bosses, it was often very nuanced. They want a very simple, are we red, yellow, green? what do you need from me? And we're like, well, let me tell you where this team is at, right? And why it's different than this team. And it took a while for our executives to understand the differences with that and why it wasn't a one-size fits all toolbox. - [Bobbie] Yeah, and I think one of the... This is a really interesting and very telling bump that we got that I think is true here. For some teams we scheduled meetings the fourth week of the month, which is great unless it's the last week of the quarter and you're a sales team, right? Obvious, right? Exactly, so just shifting that meeting one week, one way or another, game changing.
And the fourth week of the month worked for everybody else in the group, why wouldn't it have worked for that? It certainly optimized our problem to have everything focused in that space. So just a recognition that there are some real differences. I think the other one I wanna make sure we highlight here is it's really easy early in the process for accountability to be shifted entirely onto the security team, right? If there's a security team, great.
Your problem, right? Take it. And that is not the right answer, right? And if you have a set of... If you're growing relationships and you have a set of professionals, security professionals who are experts, they're happy in a very accountability driven culture where you wanna make an impact, it's easy for them to just say, yeah, I'll take that. Yeah, okay, okay. Because they don't have the experience to know that, that's not the right answer.
And so it was really important for us to reinforce to all members of the team that these are business risk decisions, there are security elements to it. We are accountable as security professionals in that space. But having a clear roles and responsibilities, accountability, coordination, action at a detailed enough level, I think was also we should have done that sooner. We worked our way through that one a bit, but we should have done that sooner. So these were I think some of the big ouches that we captured.
This isn't the only model that exists. So we thought we would take a minute and sort of talk about the sort of range of perhaps options for this kind of business interaction activity. There's a possible option here to have a centralized team, right? Have no business engagement in sort of this model that's here. And that works particularly well if you don't have a lot of security experts, right? If that's the thing that you need to pivot on is really understanding that you have very few security experts.
If you don't have any established business governance structures, right? If you have weak business governance structures that can work, and if you have in terms of a regulated landscape, there's some some opportunity there. What I find when in places where that has been the model is you over-index on the security outcomes to the expense of the business outcomes in that space. So that's one of the important things to watch for in that model.
I think the opportunity there though is if there is not deeply established business governance structure, using the security governance model to help mature the business governance model that's there as well. There is the flip side of that, right? So central security team to, oh no, the business needs to own everything, thank you very much. Very tight business control.
If you have lots of security professionals, you can distribute them throughout the business team. I think that's really a powerful model in that space. Particularly if you have a tightly, well operating business operations, right? You have business governance from top to bottom, strong alignment, then this can be a really successful way to get the business interaction and buy-in in that space. You can over-index on business outcomes there, right? Security can't necessarily have a strong voice. You need to watch for that. I've seen it done beautifully.
So this model does work and it grows security awareness in the business if done right, right? Because you've now put security in every business meeting, every business decision meeting, which I think is a win for many individuals. Then there's this model has existed in many places, right? The business is saying, I don't want you new security people, and the security guys are saying, hey, we're the security experts, do what we tell you. I don't wanna hear what's going on in your business in that model. That creates lots of duplication of effort, lots of poor communications.
But if you can flip that, right? If you can create the conversation between the two, rapid opportunities there for maturation, right? Really ripe for that kind of effort. What we had was some security expertise in place, right? And not a strong dearth of them. We had good but not exceptional business governance structure in place and we have a lot of regulation in that environment. And that meant we took this sort of federated-based approach for this particular use case. And I would say as the product group BUSO in Dell, I have all of these with different product units there. And so I have slightly different engagement models in different activities.
And I posit there might be a maturation model in here somewhere. I just haven't figured that out yet. - [Bobbie] So... - [Molly] So... - [Bobbie] Please. - [Molly] What do you do next? So if you're listening, you're going, okay, well, how do we go about starting to do this within our organization? These are just the steps that we took really with a shot clock about this time of year to really have it up and running within one year.
So from a security leader perspective, Bobbie came in and started having the discussions about what we need to do within the business, and from a business leader perspective, I started finding my change agents, my influencers within the business that were my security experts, and listening to them. That's when I became the therapist and started listening to them. - [Bobbie] Yeah, and it was important I think for both of us is it wasn't just finding a business leader or a security leader at the working level or at the senior level, right? We both have the obligation to span from the most senior executive down to the security engineer working on a... Trying to figure out how to implement a particularly specific thing. And that can be a tough span in conversations, but was really necessary in order to get the kind of traction and credibility that we needed. And so then it was about listening to what the priorities are, right? What are the business priorities that are going to be important for the next year? Is it moving into a new market? Is it from our...
Is it building out new product? Is it making relationships with different organizations? That business context is phenomenally valuable because it will give you as a security professional an understanding of what buttons to push, what doors to go to and where to avoid in each of these situations. And I think the flip side is from the business construct, understanding what the security priorities are that are set, whether it be by the board or the leadership team or by what's best practice in the industry or by the adversary there, that becomes an important element, and working through the language for that conversation. And then in a quarter... - In a quarter, that's when you start looking at the business priorities for next year.
That's when we sat down and we started looking at the team construct and making sure there was a yin and yang to both sides, right? If I'm gonna go support this, making sure Bobbie also had that capability. If Bobbie was going to put something in drive, one of the top enterprise priorities, I needed to make sure that it aligned with business priorities as well. And that's when we started talking about investments. That's when we started talking about what core competencies we needed within team members. And also making sure that as we were going to go forward, that we were going to set goals that were going to be achievable for those quick wins within the first year. So we weren't talking about boiling the ocean all in one year.
We were starting to talk about building the foundation and those really quick wins that we were gonna focus on, as well as hiring and laying the groundwork for those longer transformational things that we knew were going to be a three-year long or maybe even more journey, right? And resetting those expectations so that when we could start... - [Bobbie] Yeah, I think that's important is it wasn't just run out and hire somebody right away. It was understand first, and then figure out what the best first hires are and look for those alignments.
And so from the quarter to the year, building that sort of joint strategy and integrating the business systems for operations there. It was a fun year. I think we had a lot of roadblocks, quite a few wins. And I feel like we're right about at the point where I have faith and trust that our plan will be successful going forward. So I think we have a few minutes for...
Steven, do we have five minutes for questions? We have three minutes for questions. So if anybody has a question. - [Speaker] Yes. You've touched on this part. A corporation with Dell size, you're gonna have multiple departments, multiple business units, product security, D&E security, operations, et cetera. I'm presuming you're forming this relationship with each of these business units.
How do you maintain and who has overall accountability? Because you've mentioned shared responsibility, but you can't have shared accountability- - [Bobbie] Accountability for what? - The overall program. Is it each business unit? Is it the chief security officer- - [Bobbie] So we have a chief security officer who is accountable to the leadership team and the board for reduction of security risk, right? For clear articulation of what a security program is and reduction of security risk to the levels that the board sets in that space. The execution of that is done through shared responsibility between the central security team and these business security functions in the organization. And that's why it's important for us to go at a risk by risk level. What is the racy that we need to align here? Business leaders accept the risks where they won't be able to meet us and are accountable when they choose for whatever appropriate reason to not be able to meet the security standard that set centrally. But we set a really high bar in that regard and we have a lot of arm wrestling at very senior levels around times when a choice to exist below that bar is necessary.
- [Speaker] Okay. - [Molly] Thank you. Appreciate it. - [Bobbie] Yes, thank you all. - [Molly] (indistinct) the hall afterwards.
- [Bobbie] Yeah, we just got the hook, Rick.
2023-06-09 03:02


